Gartner, Inc. on June 14, 2017, highlighted the top technologies for information security and their implications for security organizations in 2017. Analysts presented their findings during the Gartner Security & Risk Management Summit, being held at National Harbour, MD.
“In 2017, the threat level to enterprise IT continues to be at very high levels, with daily accounts in the media of large breaches and attacks. As attackers improve their capabilities, enterprises must also improve their ability to protect access and protect from attacks,” said Neil MacDonald, vice president, distinguished analyst, and Gartner Fellow Emeritus. “Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile, and DevOps.”
The top technologies for information security are:
Cloud Workload Protection Platforms
 Modern data centers support workloads that run in physical machines, virtual machines (VMs), containers, private cloud infrastructure and almost always include some workloads running in one or more public cloud infrastructure as a service (IaaS) providers. workload protection platforms (CWPP) provide information security leaders with an integrated way to protect these workloads using a single management console and a single way to express security policy, regardless of where the workload runs.
Modern data centers support workloads that run in physical machines, virtual machines (VMs), containers, private cloud infrastructure and almost always include some workloads running in one or more public cloud infrastructure as a service (IaaS) providers. workload protection platforms (CWPP) provide information security leaders with an integrated way to protect these workloads using a single management console and a single way to express security policy, regardless of where the workload runs.
Remote Browser
Almost all successful attacks originate from the public internet, and browser-based attacks are the leading source of attacks on users. Information security architects can’t stop attacks but can contain the damage by isolating end-user Internet browsing sessions from enterprise endpoints and networks. By isolating the browsing function, malware is kept off of the end user’s system and the enterprise has significantly reduced the surface area for attack by shifting the risk of attack to the server sessions, which can be reset to a known good state on every new browsing session, a tab opened or URL accessed.
Deception
 Deception technologies are defined by the use of deceits, decoys and/or tricks designed to thwart, or throw off, an attacker’s cognitive processes, disrupt an attacker’s automation tools, delay an attacker’s activities or detect an attack.By using deception technology behind the enterprise firewall, enterprises can better detect attackers that have penetrated their defenses with a high level of confidence in the events detected. Deception technology implementations now span multiple layers within the stack, including endpoint, network, application, and data.
Deception technologies are defined by the use of deceits, decoys and/or tricks designed to thwart, or throw off, an attacker’s cognitive processes, disrupt an attacker’s automation tools, delay an attacker’s activities or detect an attack.By using deception technology behind the enterprise firewall, enterprises can better detect attackers that have penetrated their defenses with a high level of confidence in the events detected. Deception technology implementations now span multiple layers within the stack, including endpoint, network, application, and data.
Endpoint Detection and Response
Endpoint detection and response (EDR) solutions augment traditional endpoint preventative controls such as an antivirus by monitoring endpoints for indications of unusual behavior and activities indicative of malicious intent. Gartner predicts that by 2020, 80 percent of large enterprises, 25 percent of midsize organizations and 10 percent of small organizations will have invested in EDR capabilities.
Network Traffic Analysis
Network traffic analysis (NTA) solutions monitor network traffic, flows, connections and objects for behaviors indicative of malicious intent. Enterprises looking for a network-based approach to identify advanced attacks that have bypassed perimeter security should consider NTA as a way to help identify, manage and triage these events.
Managed Detection and Response
Managed detection and response (MDR) providers deliver services for buyers looking to improve their threat detection, incident response, and continuous monitoring capabilities, but don’t have the expertise or resources to do it on their own. Demand for the small or midsize business (SMB) and small-enterprise space has been particularly strong, as MDR services hit a “sweet spot” with these organizations, due to their lack of investment in threat detection capabilities.
Micro-segmentation
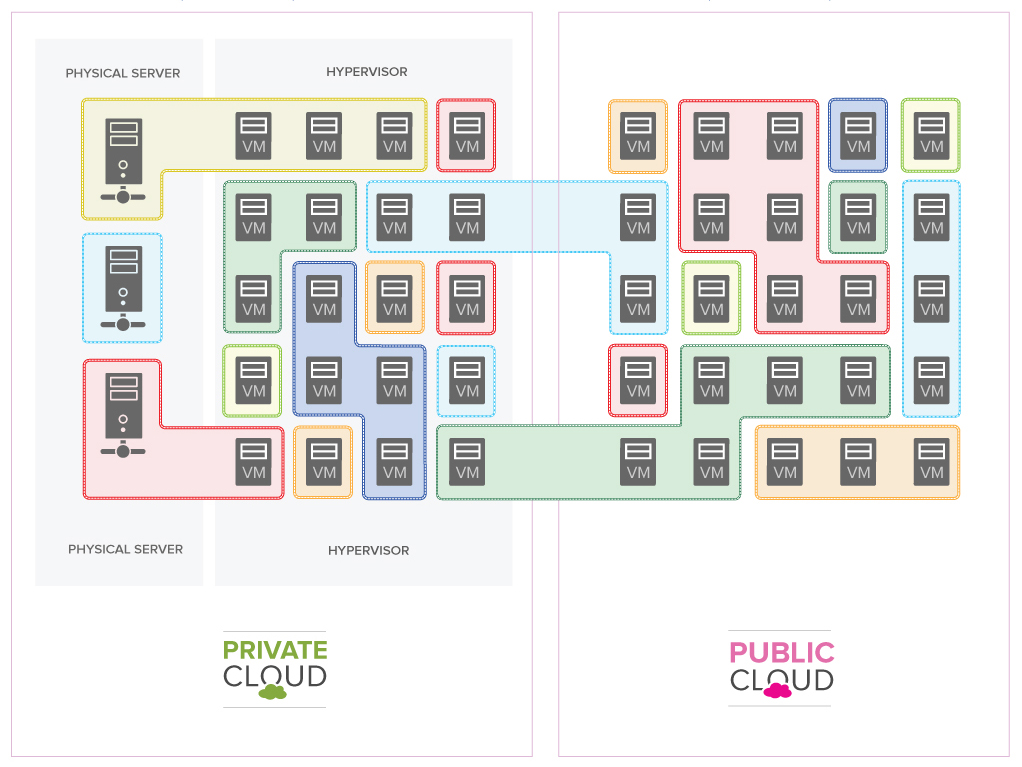 Once attackers have gained a foothold in enterprise systems, they typically can move unimpeded laterally (“east/west”) to other systems. Microsegmentation is the process of implementing isolation and segmentation for security purposes within the virtual data center. Like bulkheads in a submarine, micro-segmentation helps to limit the damage from a breach when it occurs. Microsegmentation has been used to describe mostly the east-west or lateral communication between servers in the same tier or zone, but it has evolved to be used now for most of the communication in virtual data centers.
Once attackers have gained a foothold in enterprise systems, they typically can move unimpeded laterally (“east/west”) to other systems. Microsegmentation is the process of implementing isolation and segmentation for security purposes within the virtual data center. Like bulkheads in a submarine, micro-segmentation helps to limit the damage from a breach when it occurs. Microsegmentation has been used to describe mostly the east-west or lateral communication between servers in the same tier or zone, but it has evolved to be used now for most of the communication in virtual data centers.
Software-Defined Perimeters
A software-defined perimeter (SDP) defines a logical set of disparate, network-connected participants within a secure computing enclave. The resources are typically hidden from public discovery, and access is restricted via a trust broker to the specified participants of the enclave, removing the assets from public visibility and reducing the surface area for attack. Gartner predicts that through the end of 2017, at least 10 percent of enterprise organizations will leverage software-defined perimeter (SDP) technology to isolate sensitive environments.
Cloud Access Security Brokers
Cloud access security brokers (CASBs) address gaps in security resulting from the significant increase in cloud service and mobile usage. CASBs provide information security professionals with a single point of control over multiple cloud service concurrently, for any user or device. The continued and growing significance of SaaS, combined with persistent concerns about security, privacy, and compliance, continues to increase the urgency for control and visibility of cloud services.
OSS Security Scanning and Software Composition Analysis for DevSecOps
Information security architects must be able to automatically incorporate security controls without manual configuration throughout a DevSecOps cycle in a way that is as transparent as possible to DevOps teams and doesn’t impede DevOps agility but fulfills legal and regulatory compliance requirements as well as manages risk. Security controls must be capable of automation within DevOps toolchains in order to enable this objective. Software composition analysis (SCA) tools specifically analyze the source code, modules, frameworks and libraries that a developer is using to identify and inventory OSS components and to identify any known security vulnerabilities or licensing issues before the application is released into production.
Container Security
Containers use a shared operating system (OS) model. An attack on a vulnerability in the host OS could lead to a compromise of all containers. Containers are not inherently unsecure, but they are being deployed in an unsecure manner by developers, with little or no involvement from security teams and little guidance from security architects. Traditional network and host-based security solutions are blind to containers. Container security solutions protect the entire life cycle of containers from creation into production and most of the container security solutions provide preproduction scanning combined with runtime monitoring and protection.
Gartner analysts will provide additional analysis on IT security trends at the Gartner Security & Risk Management Summits 2017 taking place in Tokyo; Mumbai, India; Sao Paulo; Sydney; London; and Dubai. Follow news and updates from the events on Twitter at #GartnerSEC.
Visit the Gartner Digital Risk & Security hub for complimentary research and webinars.
Gartner clients can learn more about security & risk in the Gartner Trend Insight Report “Digital Trust — Redefining Trust for the Digital Era.”

